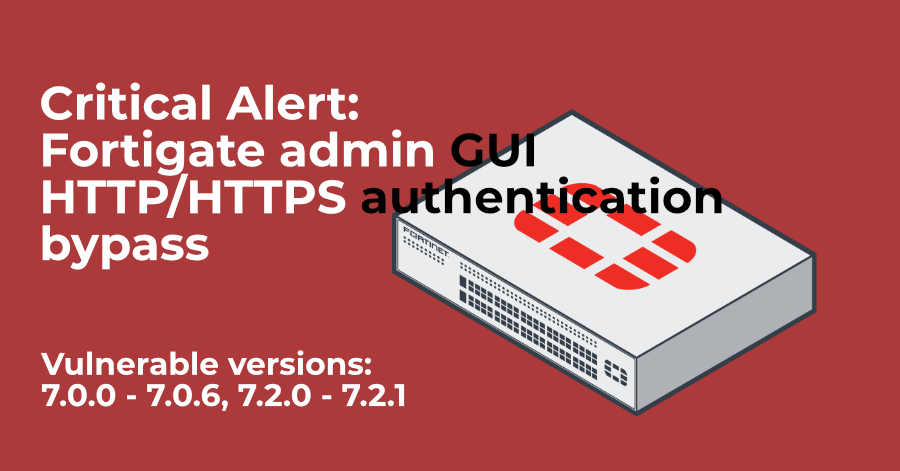
Fortigate administrator GUI authentication bypass critical vulnerability CVE-2022-40684 found
On 6th of October 2022, the Fortinet started circulating internally and to their
clients preliminary alert that admin GUI vulnerability had been found. They
released more details by now, but the whole picture regarding the exploitation
path is not known yet. The vulnerability was assigned severity 9.6 (very high),
and as far as we can understand from their bulletin - allows attackers to bypass
the administrator authentication mechanisms and get access to the GUI. Also, not
stated directly, but understood - the `trusthost` configuration does NOT
prevent attackers coming from IPs not on the trusthost list. It is now
known that if any admin-level account has 0.0.0.0 as its trusthost set, then
such Fortigate is vulnerable from any IP.
Fortinet recommend the following to be done immediately:
-
Upgrade the affected versions: 7.0.0 - 7.0.6, and 7.2.0-7.2.1 to the next available (7.0.7 and 7.2.2), as a solution.
-
Configure/duplicate specific IP addresses from
trusthostsettings (if already in place) in Local-in policy, limiting management GUI access to the trusted by you IPs, as a work around. -
Disable admin GUI HTTP/HTTPS access on Internet-facing interface(s).
To exploit this vulnerability, an attacker has to send specially crafted HTTP request. It is not known, unfotunately, how complex (or not) the exploitation is.
The Fortinet designation for this vulnerability is:
FortiGuard ID: FG-IR-22-377 CVE ID: CVE-2022-40684 Severity: Critical / CVSS: 9.6
Additional resources
Follow me on https://www.linkedin.com/in/yurislobodyanyuk/ not to miss what I publish on Linkedin, Github, blog, and more.