Fortigate - enable e-mail as a two-factor authentication for a user and increase token timeout
I'll say outright that FortiToken (be it a mobile app or a physical token) is the most secure and preferable way today for multi-factor authentication. The other two - SMS message and e-mail message are vulnerable to many attacks, including not so technically sofisticated SIM swapping. But sometimes less secure method is better than none. Two catches with using an e-mail as MFA on Fortigate though:
- It is not availabe in the GUI until you turn it on at the CLI.
-
e-mails tend to get delayed sometimes, and the default validity time for any Fortigate produced token code (SMS, e-mail, FortiToken) is 60 seconds. If user doesn't enter the token code within 60 seconds of issuing - code becomes invalid. It is usually not a problem, but recently I had to enable e-mail MFA for the client's branch in remote location with substantial e-mail delays being a norm. So optionally below you can find how to increase the default timeout.
-
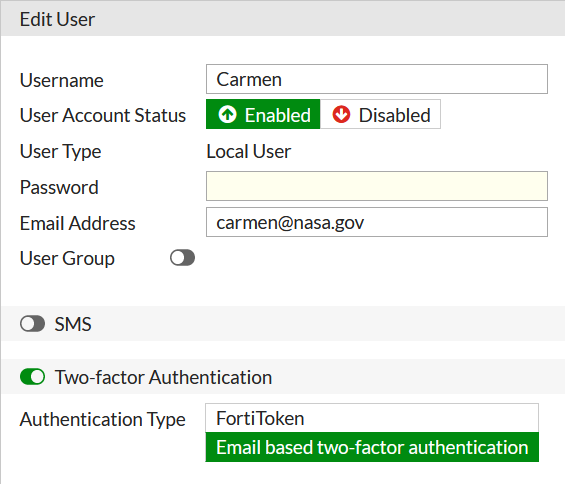
Enable e-mail option as MFA for a user:
config user local
edit "Carmen"
set type password
set two-factor email
set email-to "carmen@nasa.gov"
next
end
- (Optional) Increase token code validity from 1 to 2 minutes:
FG2 # config system global
FG2 (global) # set two-factor-email-expiry ?
two-factor-email-expiry Enter an integer value from <30> to <300> (default = <60>).
FG2 (global) # set two-factor-email-expiry 120
Additionally, we have to increase the default time of 5 seconds the Fortigate will wait between asking for the one-time code and user entering it. This configuraiton, btw, sets authentication timeout for ANY remote server authentication - LDAP, Radius etc.
config sys global
set remoteauthtimeout <1-300>
The default is 5 seconds.
Now the option for e-mail as 2-factor authentication appears in GUI:
And if not set already, of course, configure mail server that Fortigate will use to relay mails with OTP:
config sys email-server
set reply-to fgt1800F@mydomain.com
set server 3.3.3.3
end
Follow me on https://www.linkedin.com/in/yurislobodyanyuk/ not to miss what I publish on Linkedin, Github, blog, and more.