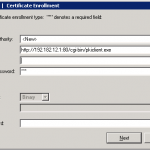
If you didn’t notice Cisco IOS routers can serve as CA servers as well. The example configurations are easy to find on the cisco.com but the only trick to know when enrolling Cisco VPN client with IOS CA is the syntax you put as url – the string should look:
http://192.182.12.1:80/cgi-bin/pkiclient.exe
I attach below screenshot so you can see what I mean.
Some references as well .
yurisk.info
Yuri Slobodyanyuk's blog on IT Security and Networking sharing experience and expertise
Category: IOS Cisco (page 1 of 3)
Here is a feature that will save you time and frustration in many possible scenarios – especially when managing Cisco routers in multi-user environment. Once enabled archiving saves periodically copy of the running configuration of IOS router to the flash or remote server. So
next time something stops working after changes and you don’t know which one caused this – just revert back to the working configuration that is readily available.
guten Tag everyone, today i am posting the video showing how to configure Dynamic Virtual Tunnel Interface (DVTI) on Cisco IOS router. DVTI for remote access has been available for a long time already and actually comes to gradually replace the old way of dynamic crypto maps, but as always people are hard to get out of the rut so mainly this great feature goes unnoticed.
In this specific setup I am using DVTI for hairpinning – i.e. I will connect using CIsco VPN client to the router and will tunnel ALL of my traffic through this connection, no split tunnel.
The main benefit of DVTI here is that using DVTI interface I can assign it ip nat inside and router will take care of NAT translating my traffic when sending it clear text to the Internet.
Enjoy
As always you can watch all my videos on Vimeo – vimeo.com/yurisk.info, also you can download there videos as files.
Reference on Cisco: DVTI on CIsco.com
You never know where your router may end up . It may be RMA’ed without proper wiping the configuration first, it may be plain simple stolen. In any of these or other unfortunate cases the last thing you would want is for the attacker get passwords or other security information stored on the router.
One piece of such information is preshared key(s) , that by default are stored in clear text.
To address this potential threat Cisco, starting IOS 12.3, provide AES encryption feature on IOS routers to encrypt the stored preshared keys. In video below I recorded you can see the walkthrough to enable and manage this security feature.
Enjoy. As always suggestions, critics, comments are welcome .
NB – Narration is in English.
Good evening everyone,
Today a colleague of mine asked if I had a ready-to-use template to schedule a reload of Cisco IOS router .
– “Of course, piece of cake, there should be millions of hits on it in Google” , was my thought. So, after 30 minutes of searching the mighty G and being surprised to have found nothing I dragged from my notes this recipe dated 2007 but still valid as ever.
Enjoy.
NB Word of warning to those trying to do it with built in KRON service of IOS – rebooting a router requires to answer “yes” at the CLI prompt and therefore will NOT work with KRON, only EEM can do it.
IOS used and tested – IOS 12.4T
Edge(config)#event manager applet ReloadMe
Edge(config-applet)#event timer cron name ReloadMe cron-entry “05 09 * * *”
Edge(config-applet)#action 33 reload
wr mem
This will reload router every day at 09:05, for other formats see man page for cron in Linux
….
event manager applet ReloadMe
event timer cron name ReloadMe cron-entry “05 09 * * *”
action 33 reload
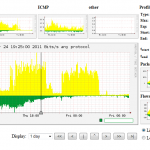
Not much of a post but link to the Cisco site stating how much Netflow loads the Cisco routers:
I, personally, do a lot of Netflow monitoring and can say that on unloaded routers , passing 2-5 mbits/sec of traffic, the additional load will be some 1-2% of CPU cycles. For the most loaded pair of routers I do monitoring for , two Cisco 2800 passing about 70 Mbits/sec of traffic and creating about 900 Mbytes of Netflow data a day each, enabling Netflow added 8% of CPU load and they cope with it perfectly well.