User actions accountability is one of the building blocks of Non-repudiation in Security.
In Checkpoint , nevertheless, the default (and widely used) user authentication for SSH and WEBGui sessions is local. Actually Checkpoint thought about that long ago and have been offering Radius authentication for users accessing the SecurePlatform via SSH or WEBgui for quite long time. I’ll put the discussion why they did it as a separately priced feature aside.
But if you have SecurePlatform Pro license for NGX R65 or earlier or Advanced Networking Blade for R70 or later then you can use it once Pro features are enabled on the SPLAT.
To help you configuring this I recorded this video , so be secure and enjoy.
PS As always feedback is welcome here as well as to the email yuri@yurisk.info.
Direct link to Vimeo
yurisk.info
Yuri Slobodyanyuk's blog on IT Security and Networking sharing experience and expertise
Category: Checkpoint NG/NGX/GAIA (page 3 of 10)
SNMP version 3 has been with us for so many years but so very few Checkpoint folks use it that I decided to do this screencast/video showing how to enable and use SNMP v3 in Checkpoint firewall. NOTE – the language of narration is Hebrew .
BTW I think of posting more videos like that . All of them will be available under http://vimeo.com/yurisk
BTW2 If you have free user in Vimeo.com you can download the videos as files as well.
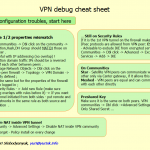
I love cheat sheets. Once I learn some product or technology to the level of understanding how it works I find the cheat sheets with all the options to run it and keep it handy. In case of the Checkpoint firewalls such cheat sheets are pretty much absent so I will throw from time to time here cheat sheets from me.
NB And to those claiming you need to know (read – memorize) everything, send them to Albert Einstein quote that when asked what the speed of light is, answered “I don’t memorize things that can be found in any reference”.
Today I’ll do VPN debug , basic stuff, no thrills. But we all started somewhere.
Checkpoint VPN debug cheat sheet
Hi everyone, in this video I tell and show how to enable SCP file transfer in Checkpoint firewall. I am beta testing it at the present therefore a bit shy to present to the wide audience, but be sure to check later when this idea of my site goes public . Thanks and see you soon.
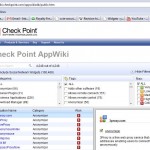 Recently Checkpoint introduced new feature on their website – AppWiki that lists with short but informative descriptions lots of software they deem interesting enough.
Recently Checkpoint introduced new feature on their website – AppWiki that lists with short but informative descriptions lots of software they deem interesting enough.
Even more of goodies – it is public. Since I learned about this cute resource I don’t waddle through the zillions of pages in Google for say Twitter client 😉 – I go straight to the AppWiki from Checkpoint and pick the one I like. To showcase I attach the screenshot of the website.
Thanks guys and gals and Happy New Year everyone.
 Well, saying ‘present’ I was a bit sarcastic – just another release in the NGX family – R75 , that is now available for download: R75 release .
Well, saying ‘present’ I was a bit sarcastic – just another release in the NGX family – R75 , that is now available for download: R75 release .
So go ahead , install it , use it, enjoy its new features and bugs and report back to the mothership .
Note At the present trial download of R75 is not available but you can download R71.10 that isn’t that different . The usual way to go – Trial software from Checkpoint.